The vulnerability of mobile devices is becoming a more serious problem with each passing day. Technological progress has generated a huge number of smart technologies that are sometimes being used against us.
There are lots of not interesting emails from services and stores or letters from strangers we receive every day. Invisibility on the web? Advertisers have certainly not heard about it. If you have already encountered a similar phenomenon, most likely part of your personal info has leaked to the network. How does this happen and how to defend yourself?
Privacy Policy in Nowadays World
Large corporations periodically inform their clientele about data leakage as a result of hacker attacks or critical system errors. If corporate and government agencies cannot ensure the security of your info, then you should find out how to defend yourself on your own on Cooltechzone.com.
Protecting confidential data in an era of information technology rapid development is a priority for every person. With the growth of portable devices’ productivity, a large amount of personal data is accumulated and used. Smartphones based on Android and iOS offer a convenient ecosystem for interacting with the global network but do not guarantee the complete security of confidential data.
Three best ways to defend your smartphone:
-
Use data encryption
In modern smartphones, part of the data is encrypted by default, but to ensure complete protection of info on the internal memory and external drive, the security settings of the mobile device provide the ability to bind encryption to a personal password. You will have to enter the selected combination of characters each time you turn on or unlock the device depending on the selected security settings. Securing confidential data through built-in encryption algorithms is carried out in a few clicks. This guarantees the security of info even in case of a permanent mobile device loss.
-
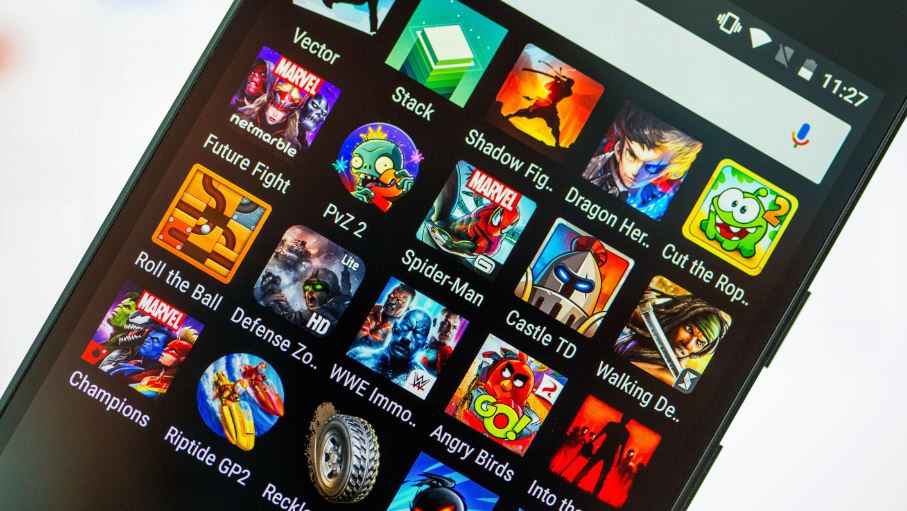
Pay attention when an app is asking for permission
Downloading applications from trusted sources such as Google Play does not guarantee the absolute security of your data. Before the final installation, you must familiarize yourself with the list of permissions that the application requires. Large corporations collect your data only to improve the users’ interaction with their product, not to sell the info. Having made the right choice, you can maintain a high level of data protection and not worry that unscrupulous developers will get confidential info without your consent. Trust proven enterprises that have been creating apps for iOS and Android for years.
-
Use VPN service
Installing the application with a paid VPN service takes the protection of confidential smartphone data to a whole new level. A lot may be said about what a VPN is, but we will only go over the facts.
Pros of VPN
Utilizing VPN technology on your mobile device enables you to:
- hide IP address and location;
- encrypt traffic using the AES-256 algorithm;
- unblock access to websites and services;
- circumvent government censorship.
To safeguard your smartphone from internal and external threats, you need to use the built-in security features of the device, configure application rights, and use the VPN service that supports modern traffic encryption technologies.
Private companies are investing enormous funds in the provision of the ultimate level of security. Download applications from reliable sources, do not neglect the built-in capabilities of modern mobile operating systems, and opt for a reliable VPN with a transparent financial policy.
Why Protect IP Address
Any experienced specialist can easily track user activity by IP address. This is done by compiling logs of visited sites, as well as when messaging and posting content. Therefore, all of our online activities are visible to providers. Knowing how to hide an IP address is important even for those who have nothing to hide. After all, the IP address is personal data, and its use should be regulated by the information privacy law.
The general regulation on data protection adopted in the EU regulates the use of addresses in the countries of the organization. There is always the risk of breaking the law, so no one can guarantee that your IP address will not be compromised. And that’s why it’s important to know how to hide the IP address. What can happen?
Unfortunately, attackers who hunt for personal data are always wide awake. They can use the information in many ways. At times, IP addresses are used by advertising companies; as a result, all kinds of ads are sent to the user’s email. But this is not the worst scenario. That’s why you should know how to hide an IP address – these are the most common consequences you can face:
- Knowing how to hide an IP address, you can circumvent censorship. Whereas the Net has traditionally been considered a territory of freedom and openness, it is under increasing pressure from authoritarian governments and large business structures. Users are often faced with blocking their favorite websites. Some companies are thus trying to fight competitors.
- Illegal content downloading. Often, criminals post counterfeit or obscene material on the Internet using someone else’s IP addresses. Thus, they are trying to deflect blame and shift responsibility to innocent users. Hiding the IP address, you can protect yourself from undeserved blocking, not to mention the bigger problems.
- Large Internet companies (YouTube, Google, etc.) analyze user activity, preferences, and send out personalized ads based on these data. This does not do much harm, although at times it irritates.
Any paid or free VPN service involves building a secure channel between your device and the VPN through which your traffic passes before accessing the worldwide network. As a result, your real IP address will be invisible to third parties. This will make it much harder to spy on you. Mind that your personal data is available for VPN services. Remember that VPN for Android, iOS, and PC makes it feasible to encrypt all data transmitted to the Net for free – this is a powerful factor in how to safeguard private data and ensure invisibility on the web.
If you are facing any problem continuously with the hardware or software part of your phone, You can also go to phone repair near you to fix any problems. Before get into the shop you have to encrypt and let it be repaired by any specialist.